A Taxonomy of the Standardized Vocabulary of 2026 Breach Disclosures : There is a genre of corporate communication that, after twenty years of observation, has stopped pretending to be communication and has become liturgy. It is the post-incident statement. In the first months of 2026 alone, I have read at least thirty of them. They were, with minor lexical variations, the same statement.
This article is a brief taxonomy of the genre, an analysis of its four sacramental phrases, an examination of recent examples, and a closing reflection on what the recurrence of the genre is telling us about the state of cybersecurity governance.
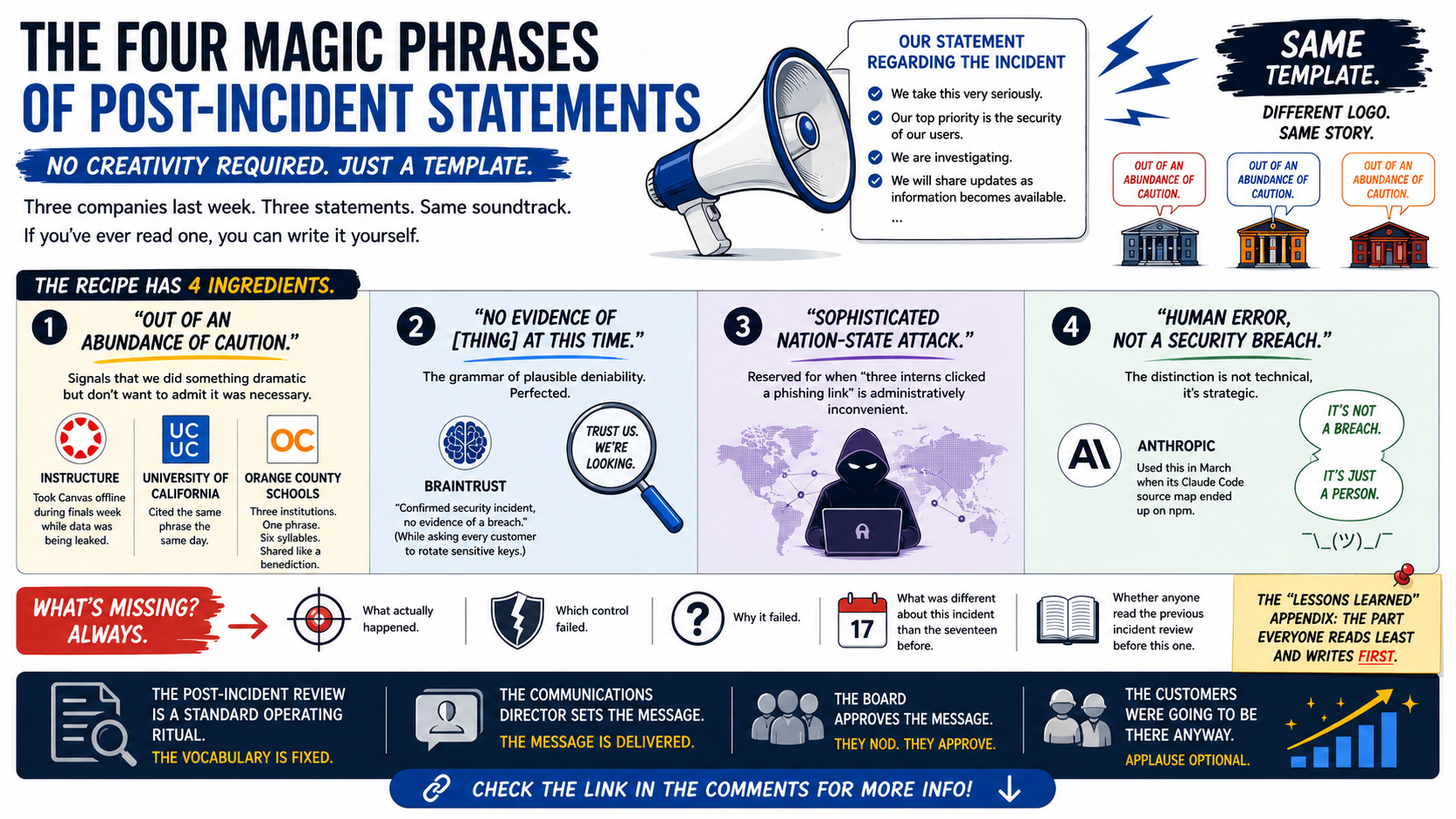
The Four Sacramental Phrases
The post-incident statement, in 2026, is built from four interchangeable phrases, each with a specific liturgical function.
1. “Out of an abundance of caution”
The phrase signals that the company has done something dramatic (taking a system offline, locking accounts, suspending a service) but does not want to admit that the dramatic action was necessary. It frames the response as voluntary virtue rather than required mitigation.
Instructure used the phrase, verbatim, when it took Canvas offline during the ShinyHunters extortion in May 2026. The University of California issued a parallel statement citing the same phrase, the same day, to the same effect. Orange County schools used it too. Three institutions, one phrase, six syllables shared across the country like a benediction passed between churches.
2. “No evidence of [thing] at this time”
This is the grammar of plausible deniability, refined over a decade of breach disclosure practice. The phrase says nothing about what was found. It says only what was not found at a specific moment.
The Braintrust statement of early May 2026 is a textbook case. The AI evaluation startup told every customer to rotate sensitive keys. The accompanying spokesperson statement: “confirmed a security incident, no evidence of a breach at this time.” The first half acknowledges. The second half retreats. The customer rotates the keys anyway, because the operational reality contradicts the rhetorical posture.
3. “Sophisticated nation-state attack”
This phrase is reserved for incidents where the more accurate description (“three interns clicked a phishing link”, “an unmaintained server got compromised”, “the backup credentials were committed to a public GitHub repository in 2019”) is administratively inconvenient.
“Sophisticated” elevates the attacker above the defender. “Nation-state” places the incident outside the company’s normal duty of care. The two together imply that the company was attacked by a force against which no reasonable defense could have prevailed. This is almost always untrue. The successful nation-state actor of 2026 routinely enters through the same vectors that the unsuccessful criminal of 2018 used.
4. “Human error, not a security breach”
This is the most recent addition to the genre. Anthropic used it in March 2026 when its Claude Code source map was accidentally shipped to npm, exposing roughly 513,000 lines of agent harness code. The distinction is not technical, it is liturgical. A “breach” implies an external attacker, and triggers a different regulatory and reputational machinery. “Human error” implies a Slack channel, a debrief, and a process improvement. The company doing the disclosing benefits enormously from the distinction. The customer whose data is suddenly more exposed does not particularly care which word is used.
What is Missing from Every Statement
What is missing, in nearly every post-incident statement of 2026 I have read, is the substance.
Which control failed. Why it failed. What was different about this incident than the seventeen before it. What was the same. Whether the failure mode was a known weakness in the architecture or a new failure mode. Whether the response time was within the company’s own stated targets. Whether anyone in the organization had warned about this specific class of failure before it happened, and what was done with that warning.
This information is, in most post-incident statements, replaced by the four sacramental phrases above. The replacement is not accidental. The phrases function precisely because they do not require, and do not permit, the substantive content. They are designed to satisfy the disclosure obligation without triggering the reputational, regulatory, or contractual consequences that the substantive content would carry.
Why the Genre Persists
The genre persists because the incentive structure that produced it is unchanged.
The company that issues the statement is incentivized to minimize. The communications director is rewarded for the statement that produces the least secondary news cycle. The legal counsel is rewarded for the statement that creates the least admissible evidence in future litigation. The board is rewarded for the statement that does not require a board-level intervention. The CISO is rewarded for the statement that is consistent with the prior cybersecurity posture the CISO has been presenting.
The customer, the regulator, and the press are theoretically incentivized to want the substantive content. In practice, none of them have the leverage to require it. The customer has already signed the contract. The regulator has not yet issued the enforcement action. The press has the next breach to cover by Thursday.
The result is twenty years of identical post-incident statements, twenty years of identical post-incident reviews, and a curiously stable rate of post-incident learning that hovers, in industry-wide observation, near zero.
The Strategic Cost
The strategic cost of the genre is not, primarily, that customers are misinformed. Customers, by and large, have stopped reading the statements. The cost is that the genre prevents the cybersecurity community from learning across incidents.
If every post-incident statement reads “sophisticated nation-state attack, out of an abundance of caution, no evidence at this time, human error not a security breach”, the body of practitioner knowledge does not grow with each incident. Each incident is, by the act of communication that follows it, made indistinguishable from the previous one. The lessons of the previous incident are stored in a different vocabulary, in private debriefs, on a Slack channel that the new CISO of the next victim company will never see.
The cumulative effect, across two decades, is that the cybersecurity community has roughly the same level of operational maturity as it would have if it had never communicated about its incidents at all. The communication theatre has, in net, not transferred knowledge. It has redistributed reputation.
A Note on Regulatory Pressure
The Cyber Resilience Act Article 14, applicable from September 11, 2026, will introduce a structured reporting obligation for product manufacturers that, in theory, requires substantive content. The reporting to the ENISA Single Reporting Platform is machine-readable, time-bound (24h / 72h / 14 days), and centrally aggregated. In theory, this should disrupt the post-incident communication liturgy.
In practice, what is likely to happen is that the substantive reporting will go to the SRP, and the liturgical communication will continue, unchanged, on the public-facing channels. The two streams will diverge. The CSIRT will know what happened. The customer will continue to read “out of an abundance of caution, no evidence at this time”.
This is, structurally, a step forward. The CSIRT having a real picture is better than nobody having one. But it does not address the public-facing liturgy. The communications director still has the same incentives. The press release still goes through the same review.
The “lessons learned” appendix is, in every post-incident review I have read, the section that is written first and read least. It is written first because it is required. It is read least because, in its current form, it contains no lessons.
A serious community would build a different post-incident communication genre. It would describe the specific failure mode, the specific control that failed, the specific organizational dynamic that allowed the failure, and the specific change being made. It would do this not in spite of the legal and reputational pressures but in defiance of them. The community would treat the reputational hit as the price of collective learning.
We are, demonstrably, not yet that serious community. But the next viral breach will, with high probability, be communicated in language nearly identical to the previous one. The “sophisticated nation-state attack” will strike again, out of an abundance of caution, with no evidence at this time of anything that would meaningfully change the practice that allowed the strike.
The communications director will, of course, manage it beautifully.
All my “insane” books on cybersecurity and governance are here 👉 https://www.amazon.it/stores/author/B0FB47T6Q4/allbooks