A Note on Linguistic Confusion, Threat Attribution, and the Continental European Boardroom
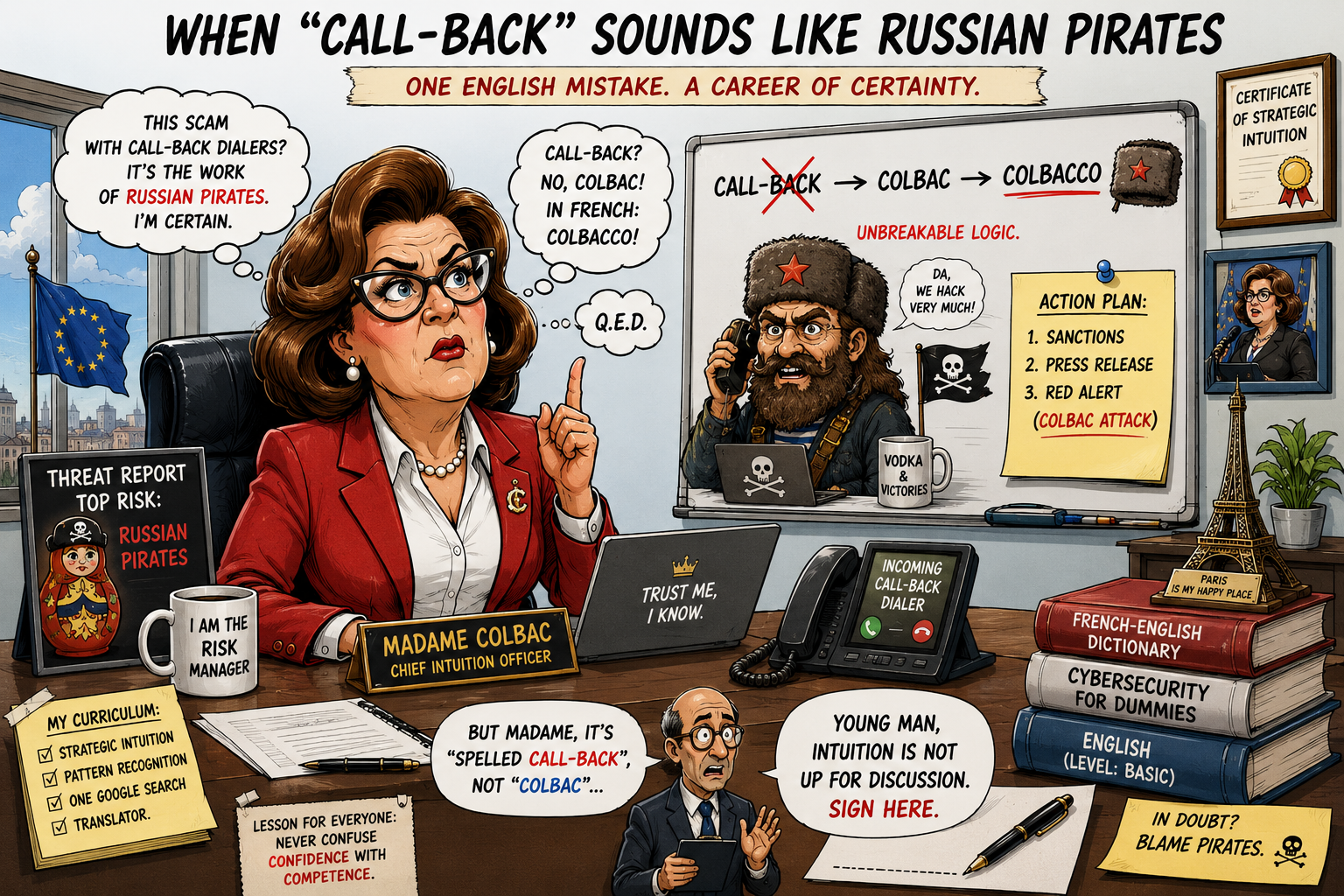
Some years ago, a senior executive at a European bank briefed her board on a cyber threat the company was facing. She referred to it, with the confidence that only comes from having read the executive summary the night before, as “a sophisticated Russian state-sponsored attack”. The internal cyber team, sitting in the back of the room, exchanged a look that contained, in its single second of duration, twenty years of accumulated experience.
The attack she was describing was a callback dialer phishing campaign. A criminal operation. Run by organized crime groups, operating through underground platforms that rent multilingual call-center agents by subscription. Volume measured in the millions per month, globally, according to Proofpoint’s State of the Phish data. No state attribution, no GRU, no nothing. Pure, scaled, criminally rented operations.
Nobody asked her why Russian. They did not need to. It took the cyber team in the back of the room about four seconds to reconstruct the etymology. “Callback”, read at the speed at which an executive reads a briefing note the night before, becomes “colbac”. In French, “colbac” is the Russian fur hat. The phonetic resemblance had, in her mental model, ceased to be phonetic and had become evidence. The Russian state actor was, technically, a hat.
She did not explain her reasoning. The board did not ask. The minutes were written. The misattribution was inscribed.
The cyber team, sitting in the back, has nicknamed her Madame Colbac ever since.
What a TOAD Attack Actually Is
Callback phishing belongs to a broader category called TOAD, for Telephone-Oriented Attack Delivery. The typical operational sequence is well documented: an email arrives, ostensibly from a legitimate vendor (Geek Squad, Microsoft, Norton, the bank itself), instructing the recipient to call a phone number to cancel a fraudulent charge or address an account issue. The recipient calls. A call-center agent, often speaking the recipient’s native language at a native level, walks the victim through a remote support session. Remote access malware is installed. The criminal network is now inside the recipient’s machine and, frequently, inside the corporate network.
The operational sophistication is not in the technology. The technology is mundane: auto-diallers, voice-over-IP, generic remote support tools. The sophistication is in the social engineering, the localization, and the scale. Proofpoint reported, in its 2024 State of the Phish, that roughly ten million TOAD attempts occur per month globally. Sixty-seven percent of surveyed businesses were affected by at least one TOAD attack in the prior year.
Whose attack is it, then. The honest answer is that it is the attack of the criminal underground that runs the call centers, the auto-diallers, and the spoofed-caller-ID infrastructure. The attribution to specific groups is possible but rarely state-level. Underground services of this kind are commercial offerings, not government operations. The customers of those services are themselves diverse: ransomware affiliates, BEC fraudsters, romance scammers, identity thieves. The attack is therefore criminal-as-a-service. Not state-sponsored. Not Russian. Just criminal, scaled, and rented.
Sources: Proofpoint, 2024 State of the Phish; Keepnet, Telephone-Oriented Attack Delivery: TOAD Explained & Defense; Intel 471, To Deliver Malware, Attackers Use the Phone.
Why the Misattribution Matters
The strategic consequence of Madame Colbac’s misattribution is not, primarily, that the board minutes contain an inaccurate threat description. The minutes can be corrected. The cyber team will, eventually, slip the correction into a footnote that nobody will read.
The consequence is that the board’s threat model now contains an entity that does not exist (a Russian state actor targeting the bank through TOAD attacks), while excluding the entity that does exist (a multilingual criminal operation that hits the bank, statistically, every quarter). The resulting risk decisions are therefore calibrated against an imaginary adversary while the real adversary continues to operate, unimpeded, against a control environment that has been resourced for a different fight.
This is not theoretical. It is the operational reality of how continental European banks have approached cyber risk for the better part of a decade. The boardroom narrative consistently overestimates state-sponsored threats and underestimates organized crime. The reasoning is partly political (state-sponsored threats are administratively legitimate, criminal threats imply that the bank has been outwitted by ordinary thieves) and partly linguistic (the executive class that runs European banks does not, in the majority of cases, have a level of technical English sufficient to follow a precise cyber briefing in its original vocabulary).
The Linguistic Gap
The linguistic gap is the part of the story that no industry report wants to write. The senior executive class of European banks operates, by selection criteria established decades ago, with a level of English calibrated to international finance, not to technical cybersecurity. International finance has its own jargon (LBO, EBITDA, NPL, RWA, CET1) which the executive class navigates fluently. Cyber jargon (TOAD, BEC, ATO, MFA bypass, callback phishing, vishing, smishing) is a separate language, recently arrived, and demonstrably more difficult to acquire mid-career than the finance jargon was when the same executives were thirty.
The result is that briefings to executive committees in continental European banks are routinely held in a register where the executives understand fewer than half of the technical terms used, and where the cyber team adapts by simplifying to the point of distortion. The distortion produces, periodically, a Madame Colbac moment. The cyber team smiles politely. The minutes are written. The risk register is updated. The wrong adversary is inscribed.
The cyber team does not correct the inscription in the moment because, in continental European corporate culture, contradicting a senior executive publicly is a career event. The cyber team also does not correct it later, in a quiet follow-up, because the senior executive has, by then, repeated the misattribution to three other senior executives, and the correction would now require asking three of them to revise their own statements. The asymmetric cost of correction relative to the cost of letting the misattribution stand is, in operational practice, infinite.
The Structural Consequence
What is missing, in the discussion of cyber risk in the European banking sector, is a serious conversation about the linguistic and conceptual readiness of the executive class for the threat picture that the cyber team is trying to communicate.
The conversation does not happen because it would be, politically, indelicate. The executive class is the one that approves the cyber budget. The cyber team that points out the linguistic gap publicly is the cyber team that does not get its budget approved the next year. So the gap persists, and the misattribution persists, and the threat model in the boardroom keeps featuring adversaries that do not exist while the real adversaries continue their monthly ten-million-attempt rhythm.
This is one of the structural reasons why DORA (Regulation EU 2022/2554), in its Article 5, places explicit accountability for ICT risk on the management body of financial entities. The Regulator has, in essence, observed that the management body is currently undertrained for the responsibility it has been assigned. The Regulation does not say this in those words. But it pushes the accountability onto the management body precisely because, until now, the accountability has lived somewhere lower in the organization, where the linguistic and conceptual capacity to handle it existed.
Whether the management body will rise to the new accountability is an empirical question that DORA implementation in 2026 and 2027 is now answering, bank by bank.
On the Archetype
Madame Colbac is, in the version told here, a satirical archetype. In the corridors of continental European banks, she is also, with minor variations in name and gender, a recurring presence. The cyber teams that brief her have, over the years, developed an entire internal genre of humor at her expense.
The humor is, at this point, mostly self-protective. The frustration that underlies it is operational: every misattribution in a boardroom is a misallocation of resources in the months that follow. Every misallocation is, eventually, paid for by a customer who is, statistically, certain to find themselves on a phone call with a multilingual criminal who is not, despite the impression in the boardroom, wearing a fur hat.
The hat fits. It is just not the hat that the attacker is wearing.
A serious banking sector would treat the linguistic and conceptual readiness of its executive class as a strategic risk in its own right. It would invest in the technical literacy of the board with the same seriousness with which it invests in the technical literacy of the trading desk. It would treat a Madame Colbac moment, when one occurred, as a structural failure of executive preparation rather than as a private joke for the cyber team.
We are, demonstrably, not yet that serious banking sector. The DORA implementation is, perhaps, the first time the Regulator has explicitly required us to become one. The next eighteen months will tell us, with the operational clarity that comes from regulatory pressure, whether we manage it.
Until then, Madame Colbac will continue to brief her board. The cyber team will continue to smile in the back of the room. And the multilingual criminal in the call center, somewhere on the Black Sea coast, will continue to dial ten million numbers a month.
All my “insane” books on cybersecurity and governance are here 👉 https://www.amazon.it/stores/author/B0FB47T6Q4/allbooks