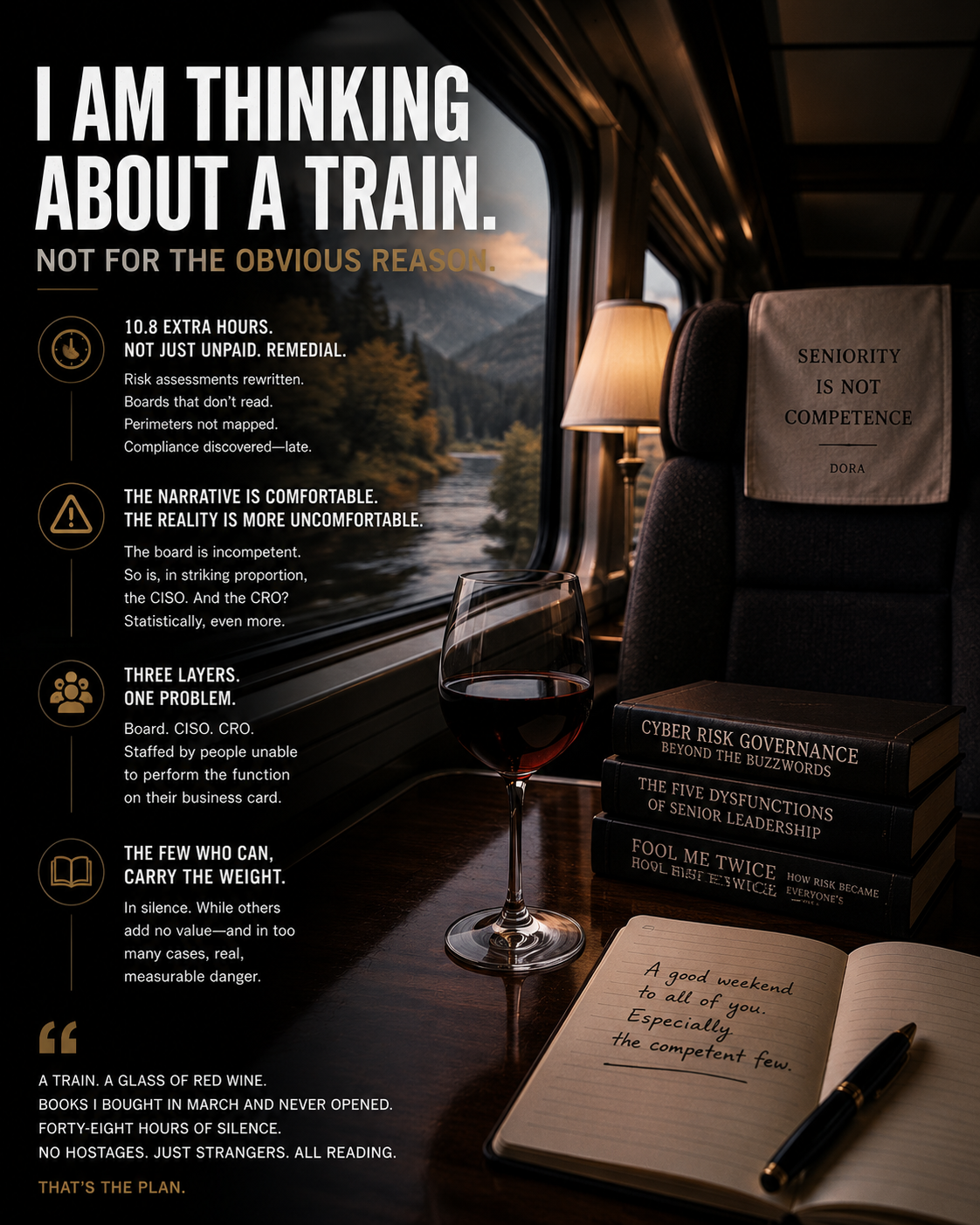
Notes from a Detached Observer of Senior Cybersecurity Governance – There is a fantasy that travels with me at the end of every working week. It is not, despite what the literature on professional fatigue suggests, the fantasy of a clean inbox. It is more specific. It is the fantasy of a train, a Friday evening, and a destination where, for forty-eight consecutive hours, I will not have to pretend, in front of a board, that the senior governance stack of European banking is staffed by people equipped for the role.
This essay is not, despite appearances, about burnout. It is about an observation, made over two decades of consulting at the senior level, that the professional class formally responsible for cybersecurity in our largest institutions includes, in a non-trivial percentage of cases, individuals structurally unable to do the job their business card claims they do.
I am, on this point, deliberately detached. I do not work inside any of the institutions I am about to describe. I work alongside them, periodically, when something has gone wrong enough that they need help that does not come from their own staff. The view from the outside of the corridor is different from the view from inside it. The view from outside is what follows.
The 10.8 Hours
A recent Help Net Security survey, published in March 2026, reports that cybersecurity professionals in the United States now work 10.8 extra hours per week beyond their contracted schedule. The framing is “burnout”. The framing is incomplete, because it does not interrogate what those 10.8 hours actually contain.
Some of those hours are work in the strict and dignified sense of the term. Incident response. Architecture review. Vendor assessment. Real cybersecurity activity that produces a real cybersecurity outcome.
The rest is something less dignified. It is remedial. It is the senior consultant who, on a Friday at 9 PM, rewrites the risk assessment because the Chief Risk Officer signed the previous version without reading it. It is the deputy CISO who, on a Sunday morning, prepares the slide deck the CISO will present on Monday, because the CISO does not, by training or temperament, know what is in the perimeter she is paid to defend. It is the senior architect who, after the third incident in a quarter, quietly explains to the audit committee that the controls described in last year’s compliance report do not exist in the production environment.
These hours are not unpaid because the professional chose unpaid charity. They are unpaid because they are repairing, in real time, the damage caused by people senior to them whose presence in the organization is justified by every criterion except competence.
The Comfortable Narrative
There is a comfortable narrative in our industry, repeated at every conference and in every “state of the CISO” report. The narrative is that the board does not understand cybersecurity, that the board needs to be educated, that the gap between board literacy and operational reality is the central problem of senior governance.
The narrative is true. It is also incomplete.
The board is, in many institutions, indeed incompetent in cybersecurity matters. Fine. The board is not, by definition, staffed by cybersecurity experts. There is no reason to expect a sitting board director, drawn from finance, law, or strategy, to have technical depth in ICT risk. The expectation would be unreasonable.
What the narrative omits, however, is the layer between the board and the operations: the CISO and the Chief Risk Officer. The board’s literacy gap is forgivable. The literacy gap of the layer that exists specifically to translate cybersecurity into governance is not.
The CISO Who Should Not Be There
A non-trivial percentage of the CISOs I have observed in mid- and large-sized European institutions over the last decade were hired through channels that, even with the benefit of hindsight, nobody can fully reconstruct, and without the technical competence the role demands. They had moderated panels. They had spoken at three conferences a year. They had written op-eds for industry publications. They had, in some cases, never run an incident response that involved more than a single weekend.
Hiring them was not a mistake of process. It was a mistake of design. The senior recruiters who place CISOs are, themselves, often unable to evaluate cybersecurity competence at depth. They evaluate visibility and surface signals, because visibility and surface signals are legible to the board that signs the offer. The CISO selected on that basis is then asked to defend a perimeter she has never operated. The unsurprising result is that, eighteen months later, the perimeter is undefended, and the consultant is on a train back from the third post-incident review of the year.
This is not a marginal phenomenon. It is structural. The pipeline that produces CISOs in 2026 produces, in addition to the genuinely competent operators, a steady supply of professionally well-presented executives whose technical depth would not survive a thirty-minute conversation with a senior penetration tester. The hiring system rewards the latter. The institution pays the cost.
The Chief Risk Officer, Statistically Even Worse
If the CISO problem is real, the Chief Risk Officer problem is, statistically, larger. The role of CRO in European banking has been used, for at least two decades, as a parking lot for senior executives who needed a title and could not, for various reasons, be given a P&L. They are not, in many cases, risk professionals. They are former heads of operations, former chiefs of staff, former heads of project portfolio, former relationship bankers whose careers had plateaued and whose departure would have been politically expensive.
Putting these executives in charge of risk does not produce risk management. It produces risk reporting. The two are not the same. Risk management requires the technical capacity to evaluate, the political capacity to escalate, and the operational capacity to redirect resources. Risk reporting requires the capacity to fill out a template and present it to the board. The role of CRO, in too many institutions, has converged on the latter.
The institutions that have understood this and have hired actual risk professionals into the CRO seat are visible from a distance. They are quieter during incidents, faster in escalation, more honest in reporting. They are also, statistically, the minority.
What This Has To Do With the Train
The train is not, despite the framing, an escape from cybersecurity. It is an escape from the theatre of senior governance, in which I have been asked to participate, weekly, for the last twenty years, on the implicit understanding that I will not say out loud what I have just said in this essay.
I will say it in this essay because the venue is mine, and because the alternative, continuing not to say it, is to participate in the theatre indefinitely, and to send another generation of competent operators into a room where they are paid to repair the damage caused by their managers and to smile while doing it.
The train, the bookstore, the quiet town, the glass of red wine, are not a coping mechanism. They are the small Friday-evening exit door from a structural problem that is currently considered unspeakable in polite professional discourse.
If I do not see you, this weekend, on a slow train heading away from the cities where boards convene, that is because I will be on a different one. A glass of red wine in front of me. The books I bought in March and never opened, finally open. A compartment of strangers, all of us silent, all of us reading, none of us, for forty-eight hours, held hostage by a gang of functional illiterates.
To the genuinely competent boards, CISOs, and risk officers reading this: you know who you are. You also know who, in your governance stack, is not. You have spent another week absorbing the cost of their presence, repairing the damage they have done without meaning to, holding the line on decisions they were technically incapable of evaluating. You have done this without recognition, often without thanks, and certainly without compensation. The pillory you carry is not a reward. It is the price of being one of the few who can do the job in a room of people who, for a long list of historical reasons, were placed at the same level as you and asked to do the same work.
A good weekend to all of you. Especially the competent few. May yours come without notifications, without board calls, without panicked Slack messages from a colleague who just realized, three months late, what NIS2 Article 21 actually requires. May it come at a safe distance from the paradox of senior governance measured in bananas, where the metric for executive standing has, somewhere along the way, decoupled from the underlying competence the title was supposed to imply.
If we end up on the same train, please let us not, on this one occasion, talk about cybersecurity. We are both off duty. We have earned, between us, exactly four hundred Friday evenings of silence on the subject. Tonight is one of them.