In the first three months of 2026, hospitals and clinics across multiple continents were forced to operate at reduced capacity, sometimes to close entirely, after ransomware groups locked down their core systems. The numbers are stark. The pattern is consistent. And the strategic question, the one no regulator has yet answered cleanly, is what happens when the target of cyber war is a place where people go to be saved.
What follows is a sober look at four data points from the first quarter, the operational reality behind them, and what they say about the moment we are in.
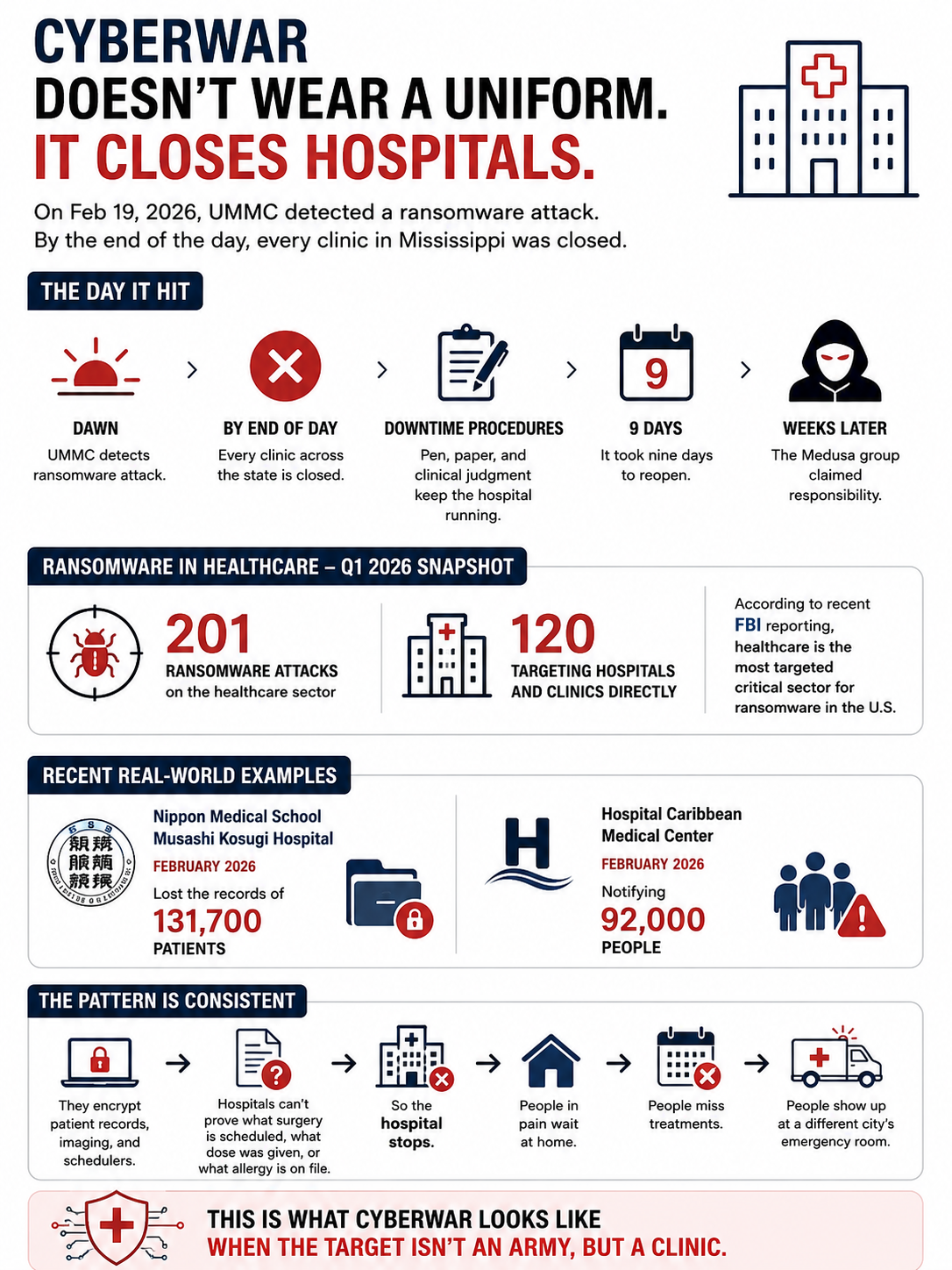
UMMC: Nine Days Without Computers
On February 19, 2026, around dawn, the University of Mississippi Medical Center detected a ransomware intrusion in its IT environment. Within hours, the institution closed every clinic across the state of Mississippi, cancelling outpatient surgeries, ambulatory procedures, and imaging appointments. UMMC operates seven hospitals, thirty-five clinics, and more than two hundred telehealth sites. Its main electronic health record system, Epic, was directly affected.
For the next nine days, the hospital ran what its staff called “downtime procedures.” That is a sober euphemism. It means pen, paper, and clinical judgment in place of dashboards, decision support, and electronic order entry. Hospital services continued, but at a fraction of normal capacity, and with a fraction of the institutional memory that a connected EHR provides.
The Medusa ransomware group claimed responsibility almost a month later, in March 2026. Investigations into whether patient data was exfiltrated were still ongoing in late April, two months after the initial attack.
Sources: HIPAA Journal, UMMC Shuts Clinics While It Grapples with Ransomware Attack, https://www.hipaajournal.com/ummc-ransomware-attack/ ; NPR, Mississippi health system shuts down clinics statewide after ransomware attack, https://www.npr.org/2026/02/21/nx-s1-5721746/mississippi-health-system-ransomware-attack ; BleepingComputer, Mississippi medical center closes all clinics after ransomware attack, https://www.bleepingcomputer.com/news/security/university-of-mississippi-medical-center-closes-clinics-after-ransomware-attack/ ; Cybersecurity Dive, University of Mississippi Medical Center reopens clinics after ransomware attack, https://www.cybersecuritydive.com/news/university-mississippi-medical-center-ransomware-attack/813507/ ; Mississippi Today, Months after UMMC cyberattack, questions persist about patient data and systems improvements, https://mississippitoday.org/2026/04/23/ummc-cyberattack-patient-data/ .
The Q1 2026 Numbers
UMMC was one of two hundred and one ransomware attacks on the healthcare sector in the first quarter of 2026. Of those, one hundred and twenty hit hospitals, clinics, and other healthcare providers directly. The remaining eighty-one targeted businesses operating within the healthcare ecosystem: vendors, billing providers, electronic health record companies, patient communication platforms, medical device manufacturers.
This split matters strategically. Direct attacks on providers force triage decisions in real time. Attacks on the supply chain force every connected provider to react simultaneously, often without knowing the full perimeter of the impact.
The change Q1 2026 documented is that attacks on healthcare-adjacent businesses rose by thirty-five percent quarter on quarter, while attacks on providers dropped by fifteen percent. Adversaries are following the path of least resistance, and that path now runs through the vendors. This is not a story about hospitals getting better at defense. It is a story about attackers reading the same threat models that defenders read, and routing around them.
Source: Comparitech, Healthcare ransomware roundup: Q1 2026 stats on attacks, ransoms, and data breaches, https://www.comparitech.com/news/healthcare-ransomware-roundup-q1-2026-stats-on-attacks-ransoms-and-data-breaches/ .
Two More Cases: Japan and Puerto Rico
UMMC made the most noise, but it was not the most exposed in absolute terms of records compromised. Nippon Medical School Musashi Kosugi Hospital, in Japan, confirmed in late February that 131,700 patient records had been compromised in a ransomware-adjacent intrusion. Hospital Caribbean Medical Center, in Puerto Rico, is currently notifying ninety-two thousand people about a separate breach in February 2026.
These two facilities sit on opposite sides of the planet, in radically different regulatory environments. They share three things. First, they are mid-sized providers, large enough to be operationally critical to a region but small enough to lack a mature cyber security operations center. Second, they suffered breaches in the same month. Third, the public reporting on both has been thin, slow, and procedural rather than strategic.
This is one of the structural problems of healthcare ransomware. Disclosure obligations exist (HIPAA in the United States, the GDPR’s Article 33 in Europe, sector-specific rules elsewhere) but they are calibrated for legal compliance, not strategic awareness. The picture you can build by aggregating disclosures is delayed, partial, and biased toward what the providers feel comfortable saying.
Sources: Comparitech (op. cit.); HIPAA Journal data breach reports.
Why Healthcare Is the Prime Target
According to recent FBI Internet Crime Complaint Center reporting, healthcare has been the most targeted critical sector for ransomware in the United States. There are five reasons that explain the pattern, and they reinforce each other.
The first is operational pressure. A hospital cannot stop. The cost of downtime is measurable not only in revenue but in patient outcomes, which means many providers, when faced with a ransom demand, decide to pay rather than rebuild. This makes the sector economically attractive for attackers, regardless of whether any individual hospital actually pays.
The second is legacy infrastructure. Hospital IT environments routinely include systems that cannot be patched without breaking a clinical workflow, devices that run end-of-life operating systems because they are certified for medical use under regulations like the FDA’s Quality System Regulation or the EU Medical Device Regulation, and integrations that span decades of acquisitions and consolidations.
The third is the size of the attack surface. Modern hospitals integrate medical devices, building automation, pharmacy automation, imaging systems, EHRs, billing systems, telehealth platforms, and third-party clinical tools. Each integration is a potential entry point, and most are owned by vendors that the hospital cannot fully audit.
The fourth is the difficulty of segmentation. In an emergency, clinical staff need access to information without friction. Strict network segmentation, while best practice, often fails in real-world hospital operations because it slows down access to information that may be life-critical. Compromises get made at the design phase that look reasonable on a whiteboard and become attack paths a year later.
The fifth is the value of the data. A medical record, with its combination of identity data, financial data, insurance data, and clinical data, sells for orders of magnitude more on illicit markets than a credit card number. Even after disclosure, the data remains useful, often for years.
Source: STAT News, Health care’s biggest cybersecurity vulnerability is structural, https://www.statnews.com/2026/04/17/health-care-cybersecurity-ransomware-project-glasswing/ ; FBI Internet Crime Complaint Center annual reports.
The Downtime Procedure Dilemma
The phrase that recurs in incident reports is “downtime procedures.” It refers to the manual fallback workflows that hospitals are supposed to have in place for moments when the IT environment is unavailable. Drug orders on paper. Manual triage forms. Manual lab requests. Manual imaging requests. Faxed referrals.
In theory, every accredited hospital in the United States and Europe maintains downtime procedures. In practice, they vary enormously in maturity. Some institutions train on them quarterly. Others have a binder somewhere that no clinical staff has opened in years. The UMMC nine-day closure is the visible end of a spectrum that includes every smaller institution that, in the same period, had to run on degraded operations because its primary systems were locked.
Two strategic implications follow.
The first is that resilience is no longer optional, and the regulatory frameworks reflect this. The Digital Operational Resilience Act (DORA, EU Regulation 2022/2554), although designed for the financial sector, sets a template that healthcare regulators are watching closely. The Network and Information Security Directive (NIS2, EU Directive 2022/2555) explicitly classifies healthcare entities as essential entities under Annex I, with corresponding obligations for incident reporting and resilience testing.
The second implication, harder to address, is that downtime procedures only work if the organization has rehearsed them recently. The cost of rehearsal, in clinical time and revenue, is real. Most institutions discount it until they need it, and by then the rehearsal is the production environment.
What Still Hasn’t Been Written
A clinic is not an army. The international legal framework for cyber operations against critical civilian infrastructure remains contested. Statements from the United Nations Group of Governmental Experts on responsible state behavior in cyberspace, and the more recent positions from the Open-Ended Working Group, name healthcare as a category that should be off-limits for state actors. Yet attribution of healthcare ransomware to state-affiliated groups is rare, slow, and politically sensitive.
The criminal economy that targets hospitals is largely Russian-speaking, well documented, and intermittently disrupted by law enforcement operations. But Q1 2026 shows that the disruption rate is lower than the recovery rate of the ecosystem. Groups like Medusa, Qilin, ShinyHunters operate in the gap between what is technically known and what is politically actionable.
What is missing, then, is not awareness. It is a doctrine. A clear statement, codified in regulation and translated into operational practice, of what a hospital is supposed to do, and what an aggressor is supposed to expect, when the target is a clinic.
Until that doctrine is written, the pattern of Q1 2026 will repeat, with regional variations and quarterly fluctuations, but with the same underlying signature. People in pain waiting at home. People missing treatments. People showing up at a different city’s emergency room. And clinicians, somewhere, opening a binder labeled “downtime procedures” for the first time.
All my books on cybersecurity and governance are here 👉 https://www.amazon.it/stores/author/B0FB47T6Q4/allbooks